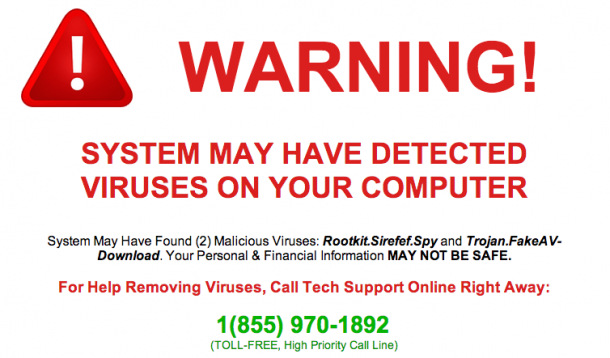
It was a dark and rainy evening when I got a frantic message to my device. It was one of our YMC bloggers. To protect the innocent, she has herein asked to be known as Ivanna Newpassword. Ivanna was in a panic. She was working on her Mac when she suddenly got a pop-up box saying that her software was infected and she needed to call the provided 1-800 number immediately. The box was accompanied by a beeping sound, the kind of repetitive ancient torture designed to break anyone. The box would not go away. The sound was relentless. Ivanna called the number.
The woman on the other end of the phone was very reassuring. She told Ivanna she could help solve the problem if she would grant the support company access to her computer. Thank goodness! Help was here.
Ivanna obliged. She was given a website to visit and was asked to download software to her computer. The support woman then took over Ivanna’s computer, analyzing it with lovely graphics and showing just how infected it was. Finally, the support woman asked for Ivanna’s credit card number so she could install the needed software to fix the computer.
It was here that Ivanna clued in that something was afoot. She declined the software and the support woman got upset. Suddenly, like the flashback scene at the end of a good movie, Ivanna realized what she had just done. She gave this woman access to her entire computer. Oh. My. God.
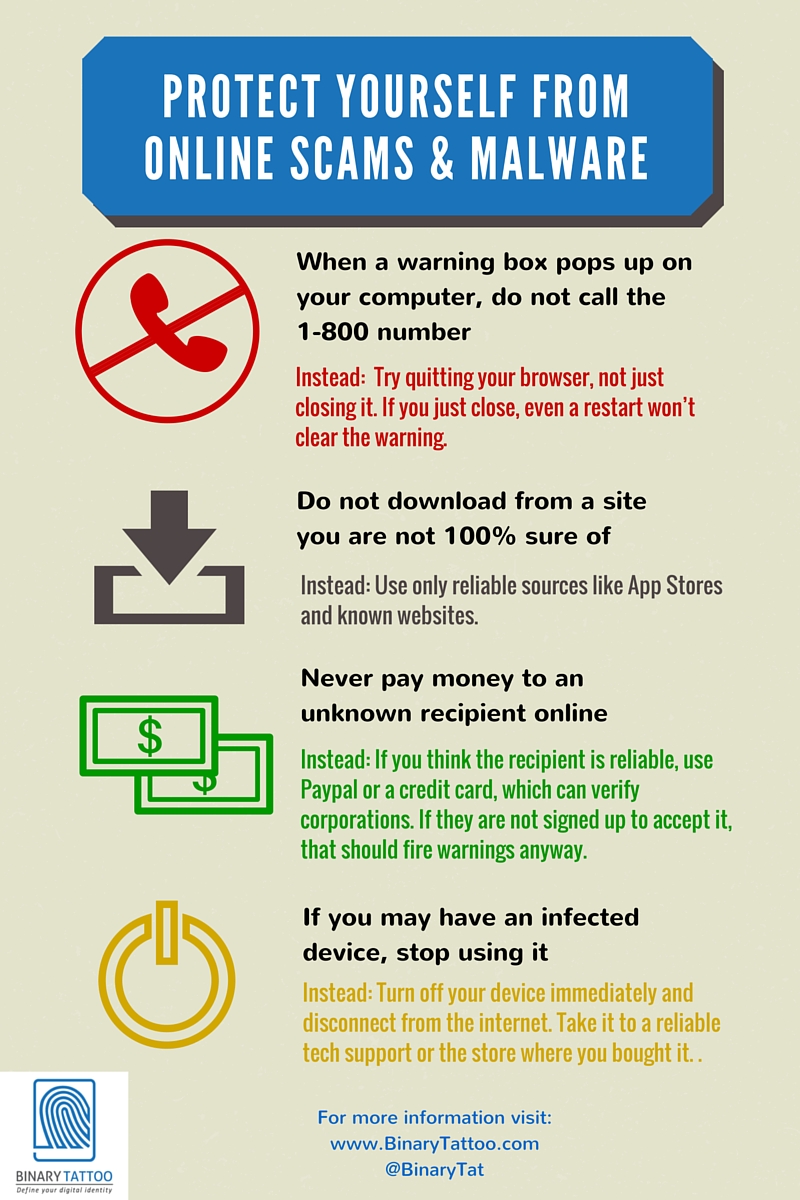
That’s when she called me. Though impossible to tell the damage over the phone, I had her disconnect her computer from the internet and close down the computer. I also suggested she log on to her email and bank accounts from a different computer and change the passwords. Having someone in your computer is like coming home after a week’s vacation to find out you didn’t lock the front door. How many people were in here? What did they touch? What did they see? What personal files did they riffle through? Did they bug the house?
When a criminal or hacker creates software for you, it is either because they want to damage your data or, more likely, they are looking for ways to get your money. If you download something malicious, it could fall in to these categories:
Malware – Short for ‘malicious software’, malware is the overall term for any software that you have on your computer/device which does something you didn’t intend it to do. It may steal your information or destroy it. It could turn on your camera or microphone to record you. It is usually disguised as something else or hitches a ride with legitimate software that you download. It is often downloaded from email attachments.
Spyware – This type of malware acts as spies do, by sitting silently on your computer watching and recording. It may log all of your keystrokes so that it can learn your passwords to other accounts. It may track your internet browsing habits. It typically sends that information back to an external source.
Ransomware – One of the newest kinds of malware, Ransomware locks your computer and charges you a ransom to unlock it again. To ensure that you don’t just trade in your device, they often steal private or personal information for bribery. The biggest case was a free porn site in the UK that secretly recorded people while they watched the porn. The scammers then ransomed the devices with the videos of the user.
Ivanna made an appointment with the Apple store for the next day to have someone look at her device in person. Turns out she was lucky. The Apple tech support analyzed her computer and deduced that the software she’d downloaded granted access to her files but nothing else. The end goal for the scammers in this story was to get Ivanna to buy the software. This said, they had access to and may have copied every file on her computer.
Let this be a cautionary tale and do not be like Ivanna! Using some basic anti-virus or anti-malware software is definitely a great idea. That said, make sure you are still taking measures to keep yourself safe.
![]() RELATED: How To Spot An Email Scam
RELATED: How To Spot An Email Scam